AWS Big Data Blog
Control access to Amazon OpenSearch Service Dashboards with attribute-based role mappings
Federated users of Amazon OpenSearch Service often need access to OpenSearch Dashboards with roles based on their user profiles. OpenSearch Service fine-grained access control maps authenticated users to OpenSearch Search roles and then evaluates permissions to determine how to handle the user’s actions. However, when an enterprise-wide identity provider (IdP) manages the users, the mapping of users to OpenSearch Service roles often needs to happen dynamically based on IdP user attributes. One option to map users is to use OpenSearch Service SAML integration and pass user group information to OpenSearch Service. Another option is Amazon Cognito role-based access control, which supports rule-based or token-based mappings. But neither approach supports arbitrary role mapping logic. For example, when you need to interpret multivalued user attributes to identify a target role.
This post shows how you can implement custom role mappings with an Amazon Cognito pre-token generation AWS Lambda trigger. For our example, we use a multivalued attribute provided over OpenID Connect (OIDC) to Amazon Cognito. We show how you are in full control of the mapping logic and process of such a multivalued attribute for AWS Identity and Access Management (IAM) role lookups. Our approach is generic for OIDC-compatible IdPs. To make this post self-contained, we use the Okta IdP as an example to walk through the setup.
Overview of solution
The provided solution intercepts the OICD-based login process to OpenSearch Dashboards with a pre-token generation Lambda function. The login to OpenSearch Dashboards with a third-party IdP and Amazon Cognito as an intermediary consists of several steps:
- First, the initial user request to OpenSearch Dashboard is redirected to Amazon Cognito.
- Amazon Cognito redirects the request to the IdP for authentication.
- After the user authenticates, the IdP sends the identity token (ID token) back to Amazon Cognito.
- Amazon Cognito invokes a Lambda function that modifies the obtained token. We use an Amazon DynamoDB table to perform role mapping lookups. The modified token now contains the IAM role mapping information.
- Amazon Cognito uses this role mapping information to map the user to the specified IAM role and provides the role credentials.
- OpenSearch Service maps the IAM role credentials to OpenSearch roles and applies fine-grained permission checks.
The following architecture outlines the login flow from a user’s perspective.
On the backend, OpenSearch Dashboards integrates with an Amazon Cognito user pool and an Amazon Cognito identity pool during the authentication flow. The steps are as follows:
- Authenticate and get tokens.
- Look up the token attribute and IAM role mapping and overwrite the Amazon Cognito attribute.
- Exchange tokens for AWS credentials used by OpenSearch dashboards.
The following architecture shows this backend perspective to the authentication process.
In the remainder of this post, we walk through the configurations necessary for an authentication flow in which a Lambda function implements custom role mapping logic. We provide sample Lambda code for the mapping of multivalued OIDC attributes to IAM roles based on a DynamoDB lookup table with the following structure.
| OIDC Attribute Value | IAM Role |
["attribute_a","attribute_b"] |
arn:aws:iam::<aws-account-id>:role/<role-name-01> |
["attribute_a","attribute_x"] |
arn:aws:iam::<aws-account-id>:role/<role-name-02> |
The high-level steps of the solution presented in this post are as follows:
- Configure Amazon Cognito authentication for OpenSearch Dashboards.
- Add IAM roles for mappings to OpenSearch Service roles.
- Configure the Okta IdP.
- Add a third-party OIDC IdP to the Amazon Cognito user pool.
- Map IAM roles to OpenSearch Service roles.
- Create the DynamoDB attribute-role mapping table.
- Deploy and configure the pre-token generation Lambda function.
- Configure the pre-token generation Lambda trigger.
- Test the login to OpenSearch Dashboards.
Prerequisites
For this walkthrough, you should have the following prerequisites:
- An AWS account with an OpenSearch Service domain.
- A third-party IdP that supports OpenID Connect and adds a multivalued attribute in the authorization token. For this post, we use
attributes_arrayas this attribute’s name and Okta as an IdP provider. You can create an Okta Developer Edition free account to test the setup.
Configure Amazon Cognito authentication for OpenSearch Dashboards
The modification of authentication tokens requires you to configure the OpenSearch Service domain to use Amazon Cognito for authentication. For instructions, refer to Configuring Amazon Cognito authentication for OpenSearch Dashboards.
The Lambda function implements custom role mappings by setting the cognito:preferred_role claim (for more information, refer to Role-based access control). For the correct interpretation of this claim, set the Amazon Cognito identity pool to Choose role from token. The Amazon Cognito identity pool then uses the value of the cognito:preferred_role claim to select the correct IAM role. The following screenshot shows the required settings in the Amazon Cognito identity pool that is created during the configuration of Amazon Cognito authentication for OpenSearch Service.
Add IAM roles for mappings to OpenSearch roles
IAM roles used for mappings to OpenSearch roles require a trust policy so that authenticated users can assume them. The trust policy needs to reference the Amazon Cognito identity pool created during the configuration of Amazon Cognito authentication for OpenSearch Service. Create at least one IAM role with a custom trust policy. For instructions, refer to Creating a role using custom trust policies. The IAM role doesn’t require the attachment of a permission policy. For a sample trust policy, refer to Role-based access control.
Configure the Okta IdP
In this section, we describe the configuration steps to include a multivalued attribute_array attribute in the token provided by Okta. For more information, refer to Customize tokens returned from Okta with custom claims. We use the Okta UI to perform the configurations. Okta also provides an API that you can use to script and automate the setup.
The first step is adding the attributes_array attribute to the Okta user profile.
- Use Okta’s Profile Editor under Directory, Profile Editor.
- Select User (default) and then choose Add Attribute.
- Add an attribute with a display name and variable name
attributes_arrayof type string array.
The following screenshot shows the Okta default user profile after the custom attribute has been added.
- Next, add
attributes_arrayattribute values to users using Okta’s user management interface under Directory, People. - Select a user and choose Profile.
- Choose Edit and enter attribute values.
The following screenshot shows an example of attributes_array attribute values within a user profile.
The next step is adding the attributes_array attribute to the ID token that is generated during the authentication process.
- On the Okta console, choose Security, API and select the
defaultauthorization server. - Choose Claims and choose Add Claim to add the
attributes_arrayattribute as part of the ID token. - As the scope, enter
openidand as the attribute value, enteruser.attributes_array.
This references the previously created attribute in a user’s profile.
- Next, create an application for the federation with Amazon Cognito. For instructions, refer to How do I set up Okta as an OpenID Connect identity provider in an Amazon Cognito user pool.
The last step assigns the Okta application to Okta users.
- Navigate to Directory, People, select a user, and choose Assign Applications.
- Select the application you created in the previous step.
Add a third-party OIDC IdP to the Amazon Cognito user pool
We are implementing the role mapping based on the information provided in a multivalued OIDC attribute. The authentication token needs to include this attribute. If you followed the previously described Okta configuration, the attribute is automatically added to the ID token of a user. If you used another IdP, you might have to request the attribute explicitly. For this, add the attribute name to the Authorized scopes list of the IdP in Amazon Cognito.
For instructions on how to set up the federation between a third-party IdP and an Amazon Cognito user pool and how to request additional attributes, refer to Adding OIDC identity providers to a user pool. For a detailed walkthrough for Okta, refer to How do I set up Okta as an OpenID Connect identity provider in an Amazon Cognito user pool.
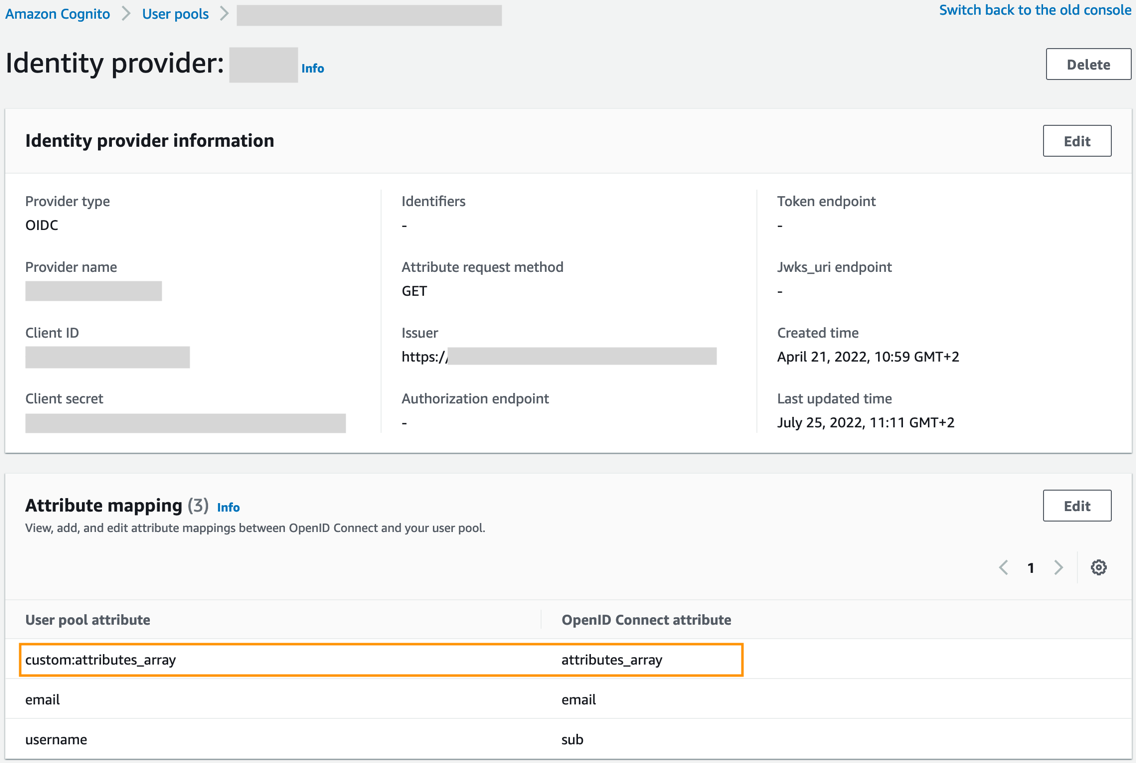
After requesting the token via OIDC, you need to map the attribute to an Amazon Cognito user pool attribute. For instructions, refer to Specifying identity provider attribute mappings for your user pool. The following screenshot shows the resulting configuration on the Amazon Cognito console.
Map IAM roles to OpenSearch Service roles
Upon login, OpenSearch Service maps users to an OpenSearch Service role based on the IAM role ARN set in the cognito:preferred_role claim by the pre-token generation Lambda trigger. This requires a role mapping in OpenSearch Service. To add such role mappings to IAM backend roles, refer to Mapping roles to users. The following screenshot shows a role mapping on the OpenSearch Dashboards console.
Create the attribute-role mapping table
For this solution, we use DynamoDB to store mappings of users to IAM roles. For instructions, refer to Create a table and define a partition key named Key of type String. You need the table name in the subsequent step to configure the Lambda function.
The next step is writing the mapping information into the table. A mapping entry consists of the following attributes:
- Key – A string that contains attribute values in comma-separated alphabetical order
- RoleArn – A string with the IAM role ARN to which the attribute value combination should be mapped
For details on how to add data to a DynamoDB table, refer to Write data to a table using the console or AWS CLI.
For example, if the previously configured OIDC attribute attributes_array contains three values, attribute_a, attribute_b, and attribute_c, the entry in the mapping table looks like table line 1 in the following screenshot.
Deploy and configure the pre-token generation Lambda function
A Lambda function implements the custom role mapping logic. The Lambda function receives an Amazon Cognito event as input and extracts attribute information out of it. It uses the attribute information for a lookup in a DynamoDB table and retrieves the value for cognito:preferred_role. Follow the steps in Getting started with Lambda to create a Node.js Lambda function and insert the following source code:
The Lambda function expects three environment variables. Refer to Using AWS Lambda environment variables for instructions to add the following entries:
- TABLE_NAME – The name of the previously created DynamoDB table. This table is used for the lookups.
- UNAUTHORIZED_ROLE – The ARN of the IAM role that is used when no mapping is found in the lookup table.
- USER_POOL_ATTRIBUTE – The Amazon Cognito user pool attribute used for the IAM role lookup. In our example, this attribute is named
custom:attributes_array.
The following screenshot shows the final configuration.
The Lambda function needs permissions to access the DynamoDB lookup table. Set permissions as follows: attach the following policy to the Lambda execution role (for instructions, refer to Lambda execution role) and provide the Region, AWS account number, and DynamoDB table name:
The configuration of the Lambda function is now complete.
Configure the pre-token generation Lambda trigger
As final step, add a pre-token generation trigger to the Amazon Cognito user pool and reference the newly created Lambda function. For details, refer to Customizing user pool workflows with Lambda triggers. The following screenshot shows the configuration.
This step completes the setup; Amazon Cognito now maps users to OpenSearch Service roles based on the values provided in an OIDC attribute.
Test the login to OpenSearch Dashboards
The following diagram shows an exemplary login flow and the corresponding screenshots for an Okta user user1 with a user profile attribute attribute_array and value: ["attribute_a", "attribute_b", "attribute_c"].
Clean up
To avoid incurring future charges, delete the OpenSearch Service domain, Amazon Cognito user pool and identity pool, Lambda function, and DynamoDB table created as part of this post.
Conclusion
In this post, we demonstrated how to set up a custom mapping to OpenSearch Service roles using values provided via an OIDC attribute. We dynamically set the cognito:preferred_role claim using an Amazon Cognito pre-token generation Lambda trigger and a DynamoDB table for lookup. The solution is capable of handling dynamic multivalued user attributes, but you can extend it with further application logic that goes beyond a simple lookup. The steps in this post are a proof of concept. If you plan to develop this into a productive solution, we recommend implementing Okta and AWS security best practices.
The post highlights just one use case of how you can use Amazon Cognito support for Lambda triggers to implement custom authentication needs. If you’re interested in further details, refer to How to Use Cognito Pre-Token Generation trigger to Customize Claims In ID Tokens.
About the Authors
 Stefan Appel is a Senior Solutions Architect at AWS. For 10+ years, he supports enterprise customers adopt cloud technologies. Before joining AWS, Stefan held positions in software architecture, product management, and IT operations departments. He began his career in research on event-based systems. In his spare time, he enjoys hiking and has walked the length of New Zealand following Te Araroa.
Stefan Appel is a Senior Solutions Architect at AWS. For 10+ years, he supports enterprise customers adopt cloud technologies. Before joining AWS, Stefan held positions in software architecture, product management, and IT operations departments. He began his career in research on event-based systems. In his spare time, he enjoys hiking and has walked the length of New Zealand following Te Araroa.
 Modood Alvi is Senior Solutions Architect at Amazon Web Services (AWS). Modood is passionate about digital transformation and is committed helping large enterprise customers across the globe accelerate their adoption of and migration to the cloud. Modood brings more than a decade of experience in software development, having held various technical roles within companies like SAP and Porsche Digital. Modood earned his Diploma in Computer Science from the University of Stuttgart.
Modood Alvi is Senior Solutions Architect at Amazon Web Services (AWS). Modood is passionate about digital transformation and is committed helping large enterprise customers across the globe accelerate their adoption of and migration to the cloud. Modood brings more than a decade of experience in software development, having held various technical roles within companies like SAP and Porsche Digital. Modood earned his Diploma in Computer Science from the University of Stuttgart.