How to use data detection and response (DDR) to gain early warning into data leakage from insider threats
Laminar Security
DECEMBER 11, 2023
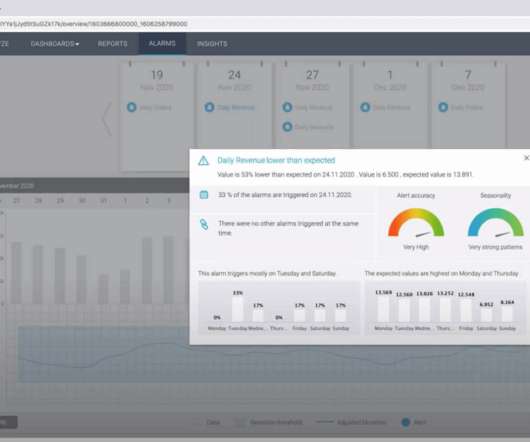
According to a report by Verizon, insider threats accounted for 30% of data breaches in 2020. Another report by the Ponemon Institute found that the average cost of an insider threat incident had increased from $15.4 DDR detects anomalous or suspicious data behavior that may indicate insider threats or other data security risks.




















Let's personalize your content