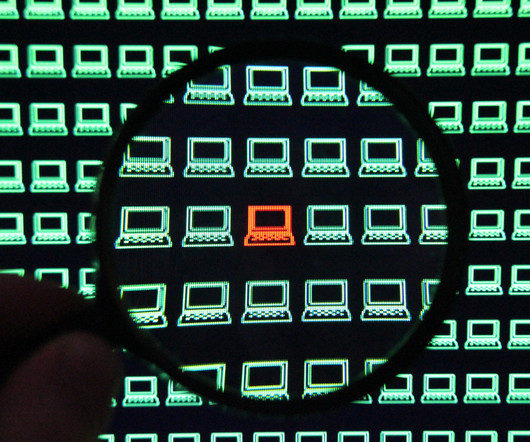
Research shows extensive use of AI contains data breaches faster and saves significant costs
IBM Big Data Hub
AUGUST 14, 2023
The Cost of a Data Breach 2023 global survey found that extensively using artificial intelligence (AI) and automation benefited organizations by saving nearly USD 1.8 This AI-powered approach can remediate both known and unknown endpoint threats with easy-to-use intelligent automation that requires little-to-no human interaction.












Let's personalize your content