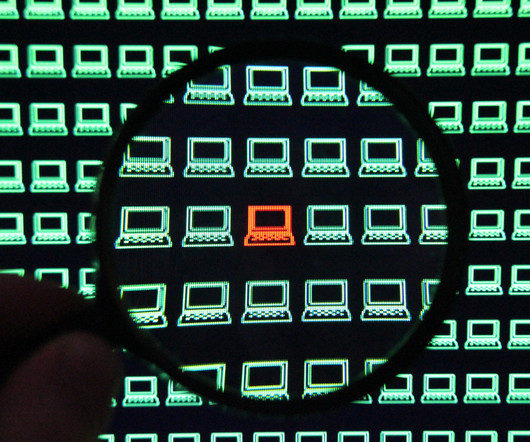
Types of cyberthreats
IBM Big Data Hub
SEPTEMBER 1, 2023
Internet of things (IOT) attack In an IoT attack, cybercriminals exploit vulnerabilities in IoT devices, like smart home devices and industrial control systems, to take over the device, steal data, or use the device as a part of a botnet for other malicious ends.










Let's personalize your content