10 projects top of mind for IT leaders today
CIO Business Intelligence
MAY 20, 2024
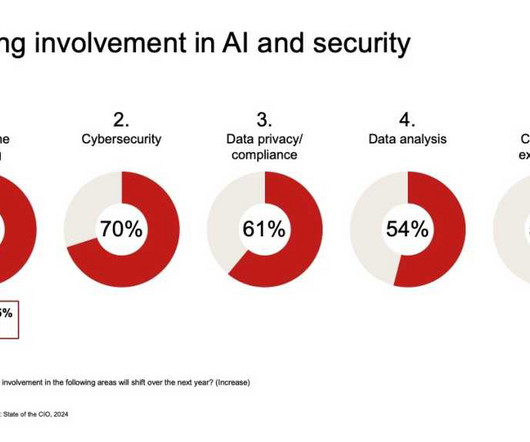
Those projects include implementing cloud-based security, anti-ransomware, and user behavior analytics tools, as well as various authentication technologies. Research from PwC had similar findings, with 47% of CIOs saying they’re “prioritizing the transformation of their data platforms to drive business growth.”













Let's personalize your content