Why You Need to Get on the Zero Trust Network Access Express Lane
CIO Business Intelligence
JUNE 23, 2022
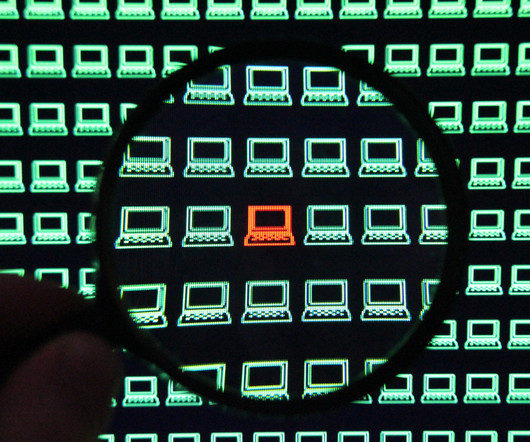
Today’s work from anywhere culture, escalating ransomware, and an explosion of Internet of Things (IoT) devices are among the trends that are driving enterprises to rethink their approach to secure network access. Behavioral analytics and least-privilege access. Like continuous authentication, ZTNA uses behavioral analytics.











Let's personalize your content