What is a phishing simulation?
IBM Big Data Hub
AUGUST 9, 2023
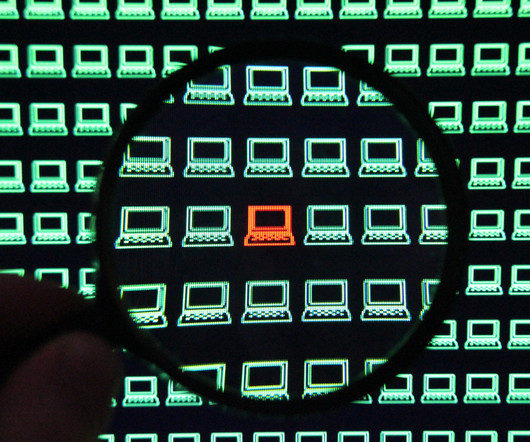
A phishing simulation is a cybersecurity exercise that tests an organization’s ability to recognize and respond to a phishing attack. Phishing tests are usually part of broader security awareness training led by IT departments or security teams. The only difference is that recipients who take the bait (e.g.,












Let's personalize your content