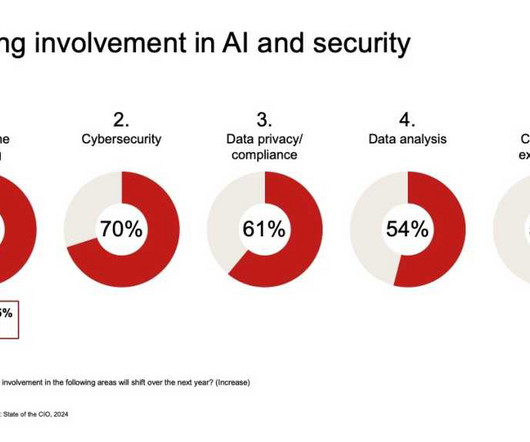
10 projects top of mind for IT leaders today
CIO Business Intelligence
MAY 20, 2024
From AI and data analytics, to customer and employee experience, here’s a look at strategic areas and initiatives IT leaders expect to spend more time on this year, according to the State of the CIO. That’s up from 85% who said as much in 2023. 1 priority among its respondents as well.















Let's personalize your content