When the Voice of the Customer Actually Talks
Rocket-Powered Data Science
AUGUST 22, 2021
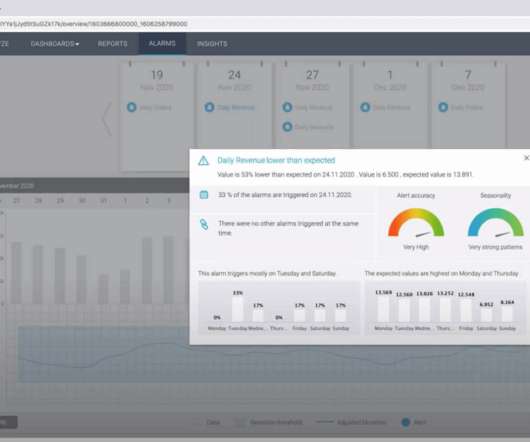
Other data sources include purchase patterns, online reviews, online shopping behavior analytics, and call center analytics. As good as these data analytics have been, collecting data and then performing pattern-detection and pattern-recognition analytics can be taken so much further now with AI-enabled customer interactions.

















Let's personalize your content