Optimizing PCI compliance in financial institutions
CIO Business Intelligence
JANUARY 4, 2024
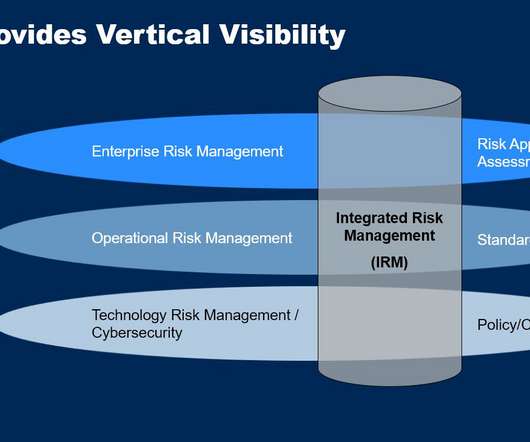
All other needs, for example, authentication, encryption, log management, system configuration, would be treated the same—by using the architectural patterns available. Consistency and risk management A security product/pattern might fulfill many security controls at the enterprise level.












































Let's personalize your content